第十七届全国大学生信息安全竞赛创新实践能力赛线上初赛个人题解
May 19, 2024 · Legacy Blog ↗
古典密码
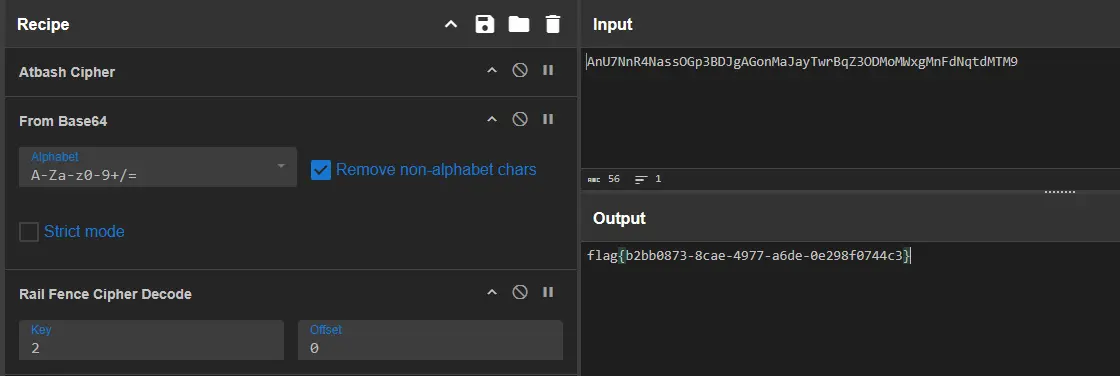
AnU7NnR4NassOGp3BDJgAGonMaJayTwrBqZ3ODMoMWxgMnFdNqtdMTM9猜测是 Base64,但是直接使用常用字母表无法正确解码,猜测还有前置步骤。尝试了常见古典加密方式后发现为 AtBash 埃特巴什码,转换后得到:
ZmF7MmI4MzhhLTk3YWQtZTlmNzQzbGdiYjA3LWNlNDctNmUwMjgwNGN9可以正常进行 Base64 解码,得到:
fa{2b838a-97ad-e9f743lgbb07-ce47-6e02804c}判断为栅栏密码,解密后得到 flag:
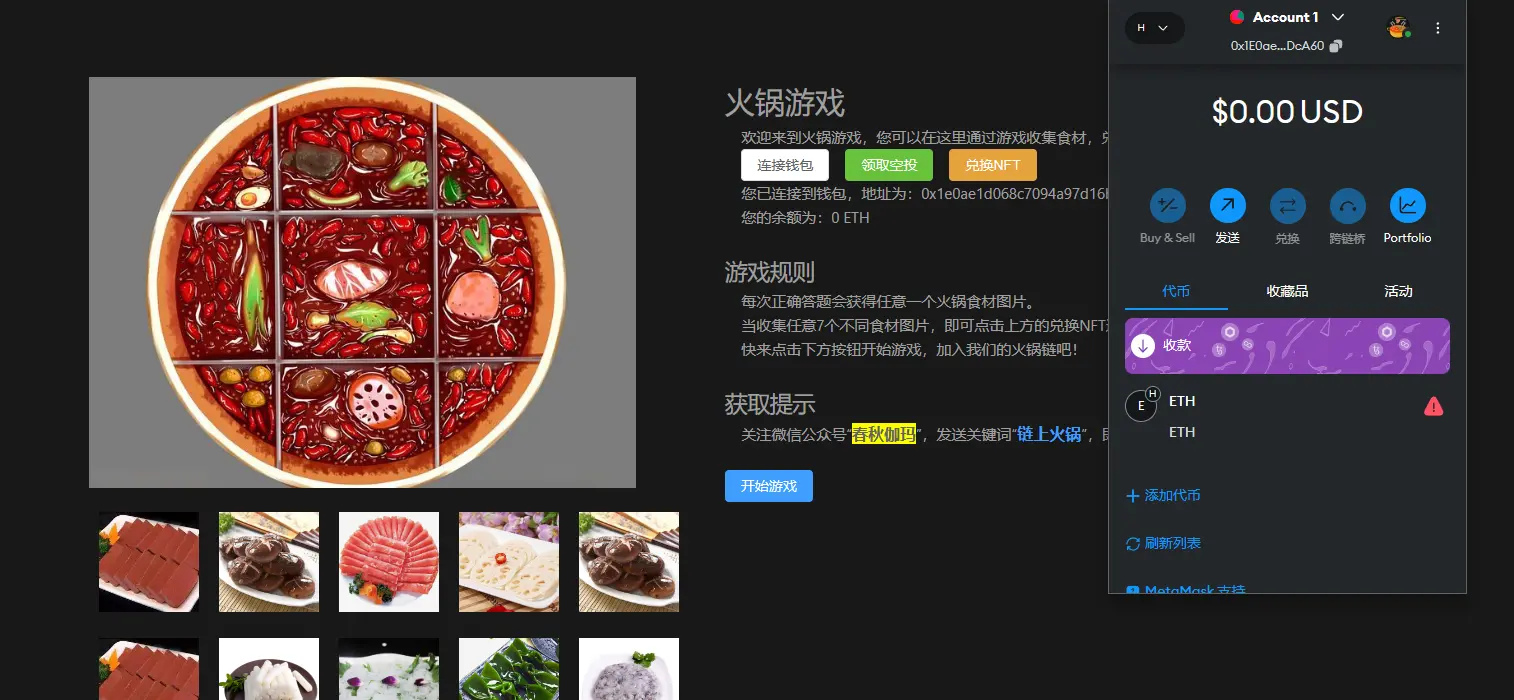
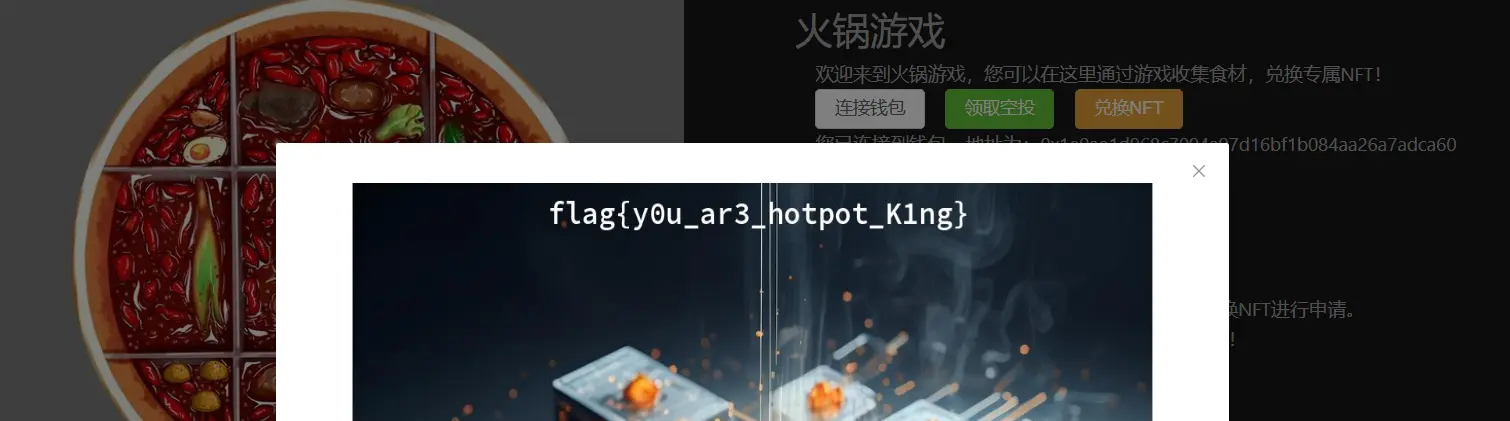
火锅链观光打卡
按照题目要求,在浏览器上安装 MetaMask 插件并创建一个钱包,然后通过网页连接到火锅链。领取空投后进行游戏,回答足够多的问题即可集齐所需的食材,兑换 NFT 即可获得 flag。
asm_re
从主函数往下跟可以发现变换部分,变换完后会和一组数据(unk_100003F10)进行比较:
__text:0000000100003C7C loc_100003C7C; CODE XREF: _main+BC↑j
__text:0000000100003C7C A9 03 50 F8 LDUR X9, [X29,#var_100]
__text:0000000100003C80 A8 03 54 F8 LDUR X8, [X29,#var_C0]
__text:0000000100003C84 AA 43 92 B8 LDURSW X10, [X29,#var_DC]
__text:0000000100003C88 08 69 EA 38 LDRSB W8, [X8,X10]
__text:0000000100003C8C A8 03 12 B8 STUR W8, [X29,#var_E0]
__text:0000000100003C90 A8 03 52 B8 LDUR W8, [X29,#var_E0]
__text:0000000100003C94 0A 0A 80 52 MOV W10, #0x50 ; 'P'
__text:0000000100003C98 08 7D 0A 1B { * 0x50 => MUL W8, W8, W10 }
__text:0000000100003C9C 08 51 00 11 { + 0x14 => ADD W8, W8, #0x14 }
__text:0000000100003CA0 AA 09 80 52 MOV W10, #0x4D ; 'M'
__text:0000000100003CA4 08 01 0A 4A { ^ 0x4D => EOR W8, W8, W10 }
__text:0000000100003CA8 08 79 00 11 { + 0x1E => ADD W8, W8, #0x1E }
__text:0000000100003CAC A8 C3 11 B8 STUR W8, [X29,#var_E4]
__text:0000000100003CB0 A8 C3 51 B8 LDUR W8, [X29,#var_E4]
__text:0000000100003CB4 AA 43 92 B8 LDURSW X10, [X29,#var_DC]
__text:0000000100003CB8 28 79 2A B8 STR W8, [X9,X10,LSL#2]
__text:0000000100003CBC 01 00 00 14 B loc_100003CC0由于前后字符互不影响,直接将所有可打印字符进行相应的处理后作为字典逆向查找解 flag:
from string import printable
table = {}
for char in printable:
cipher = ord(char) * 0x50
cipher = cipher + 0x14
cipher = cipher ^ 0x4D
cipher = cipher + 0x1E
table[cipher] = char
expected = [[0xD7, 0x1F], [0xB7, 0x21], [0x47, 0x1E], [0x27, 0x20], [0xE7, 0x26], [0xD7, 0x10], [0x27, 0x11], [0x7, 0x20], [0xC7, 0x11], [0x47, 0x1E], [0x17, 0x10], [0x17, 0x10], [0xF7, 0x11], [0x7, 0x20], [0x37, 0x10], [0x7, 0x11], [0x17, 0x1F], [0xD7, 0x10], [0x17, 0x10], [0x17, 0x10], [0x67, 0x1F], [0x17, 0x10], [0xC7, 0x11], [0xC7, 0x11], [0x17, 0x10], [0xD7, 0x1F], [0x17, 0x1F], [0x7, 0x11], [0x47, 0xF], [0x27, 0x11], [0x37, 0x10], [0x47, 0x1E], [0x37, 0x10], [0xD7, 0x1F], [0x7, 0x11], [0xD7, 0x1F], [0x7, 0x11], [0x87, 0x27]]
for value in expected:
cipher = int.from_bytes(value, 'little')
print(table[cipher], end='')
print()Tags: #CTF #Writeup #Web #CISCN
This article is authored by luoingly and licensed under CC BY-NC 4.0